In January 2020, the European Union (EU) issued a document with the resonant name “5G security Toolbox ” (5GEUtoolbox). Everyone has been waiting for the EU’s position on cybersecurity in the implementation of 5G networks, since the US ban on the implementation of 5G technologies produced in China.
Until now, the liberal EU has had a really hard nut to crack in its actions, because the regulations of the EU common market do not allow discrimination against any suppliers, and in addition, the EU must live in good economic relations with the US and China.
So let’s look at how the document “5GEUtoolbox ” allowed the EU to resolve its internal political and economic dilemma.
What is the “5GEUtoolbox” document?
The aim of the 5GEUtoolbox toolkit is to define a coordinated European approach based on a common set of preventive measures for all Member States, aimed at reducing cybersecurity threats to 5G networks. This material provides guidance for selecting and prioritizing what should be part of national and EU strategies.
The document summarizes the set of key actions by naming and categorizing the set of threats, but in particular commits to:
- Stricter security requirements for mobile network operators,
- Assessing vendor risk profiles and implementing appropriate restrictions for them with regard to critical and sensitive assets (e.g. core network functions, network management, and orchestration functions, and access network functions), and
- Introduce a multi-vendor strategy for mobile operators so as to avoid or reduce any serious dependence on a single vendor or vendors, thus avoiding a ” Vendor Lock” situation at the operator level and security at the national level.
How is the “5GEUtoolbox” structured and what areas does it cover?
“5GEUtoolbox ” was prepared as an analysis of risks related to the future of 5G technology, grouped into nine areas. For each of these areas, tools (specific guidelines) have been prepared along with an indication of how to avoid or reduce these risks through a combination of strategic decisions and technical actions (See Figure 1.).
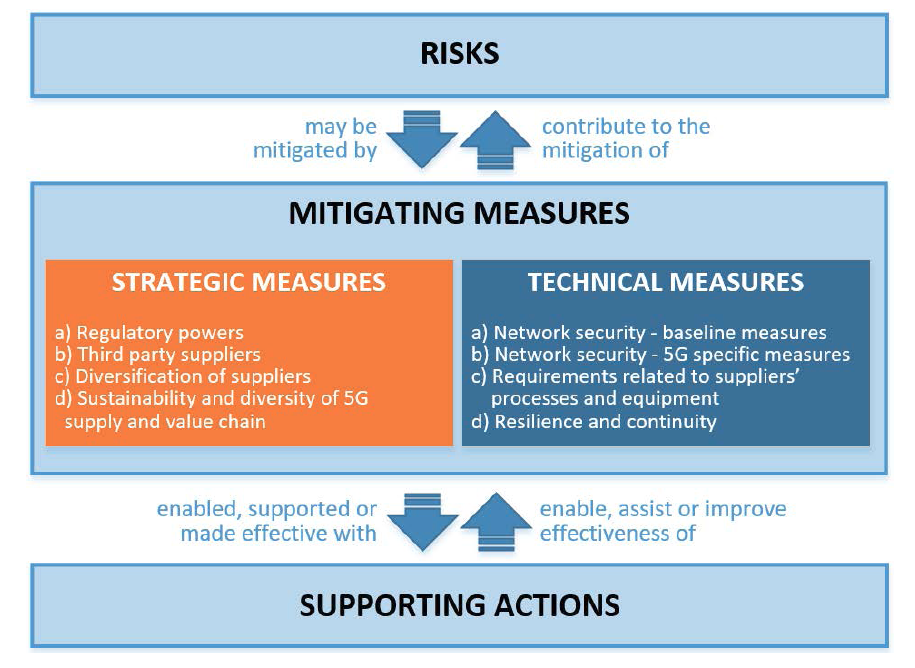
Figure 1. Flowchart (5G Risk Mitigation Measures)
Risk scenarios
The most important part of the document is the Risk Mitigation Plan, presented in the form of a table, which classifies the risks into five business scenarios:
- Risk scenario related to insufficient security measures
- Risk R1: Incorrect network configuration
- Risk R2: No access control
- Risk scenario related to the 5G supply chain
- R3 risk: Poor product quality
- Risk R4: Single supplier dependency on individual networks or lack of diversity at the national level
- Risk scenario related to the modus operandi of the main threat actors
- R5 risk: State interference in the 5G supply chain
- Risk R6: The use of 5G networks by organized crime or organized crime targeting end-users
- Risk scenario related to the interdependencies between 5G networks and other critical systems
- R7 risk: Significant disruption of critical infrastructure or services
- Risk R8: Major failure of the grid due to blackout or other support systems
- Risk scenario related to end-user devices
- Risk R9: Use of the Internet of Things, mobile phones, or smart devices
In order to mitigate the above risks, tools, so-called preventive measures, have been developed in two categories: strategic measures (SM) and technical measures (TM), and an auxiliary set of targeted support measures (SA). The risk mitigation plan maps only SM and TM measures, SA measures are only a support tool.
Risk levels
The level of risk is measured on a four-point scale:
- Very high: when the preventive measure is considered to be effective in very high and is expected, desired that almost completely reduce the associated risks.
- High: When the preventive measure is considered highly effective and is expected to significantly reduce the associated risks.
- Medium: As a preventive measure is considered somewhat effective and is expected, and desired to some extent reduce the associated risks.
- Low: When a preventive measure is considered not very effective as it is expected to reduce the associated risk only slightly.
So how to read the above scale? The higher the level (Very high), the greater the impact of strategic and technical preventive measures on individual risks. Therefore, the sooner the 5G market deals with the aforementioned risks (dark green area) using the above-mentioned measures, the sooner the security issue will be resolved.
Timeframe and risk factors
In order to prioritize, each preventive measure, two additional auxiliary categories have been introduced, namely Indicative Timeframes within which the topic should be addressed and Potential Implementation Factors which may be influenced by these procedures.
The indicative time frames for taking the necessary steps to implement the measures are expressed in the short term 0-2 years, medium-term 2-5 years, and long-term above 5 years.
Potential delivery drivers, which can be positive or negative, include resource costs, economic impacts on specific sectors (e.g. operators or suppliers), and wider economic and social impacts.
The most interesting part of the whole Table is, of course, the list of preventive measures, ie the “5GEUtoolbox ” tools, prepared by the regulator in the Risk Mitigation Plan (See Figure 2).
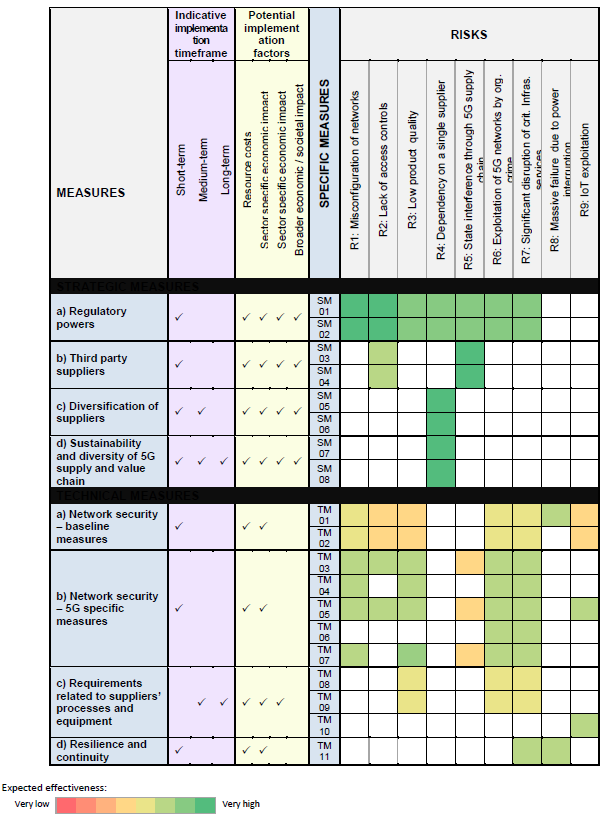
Figure 2. Risk mitigation plan
The first part covers the four areas of strategic preventive measures:
- Area Regulatory powers, which include measures SM01: Strengthening the role of national authorities and SM02: Audits of operators and information obligation for operators. Both of these tools apply to national regulators and mobile operators.
- Area External Vendors Received SM03: Vendor Risk Profile Assessment and Restrictions for High-Risk Vendors, including Necessary Exemptions to Effectively Mitigate Risk for Key Assets and SM04: Controlling the Use of Managed Service Providers (MSPs) and Support third line of equipment suppliers. As before, both of these tools apply to national regulators and mobile operators.
- Supplier Diversification area enhanced by two measures. SM05: Provide supplier diversity for individual operators through appropriate multi-vendor strategies and SM06: Strengthen resilience at the national level. As before, both of these tools apply to national regulators and mobile operators.
- The last area in this category is Sustainable Development and Diversity of the 5G Supply Chain and Value : SM07: Identifying key assets and fostering a diverse and sustainable 5G ecosystem in the EU, and SM08: Maintaining and building the EU’s diversity and capacity in network technologies. These tools concern the European Commission and the Member States.
It is therefore easy to see that strategic measures sensitize market operators and regulators to care for the diversity of 5G providers, their risk profiles, as well as the introduction of audited 5G cybersecurity systems in operators’ resources. These areas are a response to political challenges from the US administration. It is also worth emphasizing the EU’s desire to promote 5G solutions that will be developed in the European Union.
The second part of the table presents four areas for preventive technical measures :
- Network security area, basic measures where recommendations are divided into two groups. TM01: Ensuring the application of basic security requirements (secure network design and architecture) and TM02: Providing and evaluating the implementation of security measures in existing 5G standards. The first of these tools apply to national regulators and mobile operators, and the second additionally to 5G hardware and software suppliers.
- Network Security area, 5G-specific measures specifying five tools: TM03: Provide strict access control, TM04: Enhance the security of virtualized network functions, TM05: Provide secure management, operation, and monitoring of 5G networks, TM06: Enhance physical security, and TM07: Enhance integrity software, update and patch management. All these tools apply to mobile operators and national regulators.
- The area Requirements related to supplier processes and equipment are covered in the description of three tools: TM08: Raising security standards in supplier processes through solid purchasing conditions, TM09: Using the EU certificate for 5G network components, customer equipment, and supplier processes and TM10: Using the certificate EU for other non-5G ICT products and services (connected devices, cloud services). TM08: Affects national regulators, mobile operators, and providers. TM09 and TM10 relate to national regulators, the European Commission, the EC Cybersecurity Security Agency (ENISA), and Stakeholders.
- Final area: Resilience and Service Continuity with one TM11 tool: Strengthening Resilience and Service Continuity Plans. This tool applies to national regulators, mobile operators, providers, and critical infrastructure operators.
Scenarios in practice
Let us examine a couple of solutions from the Risk Mitigation Plan, using the example of the highest risk of dark green:
- The first example is the following risks: R1, i.e. Wrong network configuration, and R2 No access control, for which it is required to enter SM01 and SM02. The table shows that these are risks to be removed in up to 2 years, and they relate to the work of the national regulator, which should impose stricter obligations on mobile operators in the areas of 5G network security and audit mobile operators or require reports on network audits from them. In addition, operators will need to provide detailed and timely information on their plans to procure 5G equipment and engage third-party suppliers.
- The second example is R4 risk, ie Single supplier dependency on individual networks or lack of national diversity. For this risk, measures SM05, SM06, SM07, and SM08 have been proposed. In practice, this means the need for mobile operators to implement multi-vendor strategies in each area of the 5G network. For a proper balance at the national level, the same is to ensure incident resilience with a single operator. It is essential to introduce a system for monitoring foreign direct investment in the 5G value chain at the EU level and to develop a policy that will create conditions for European companies with support for innovation in key technology areas. This is to promote a diverse, sustainable, and safe European 5G ecosystem. For these activities, market players are even more than five years old.
- The third example is R5, i.e. State interference in the 5G supply chain. Preventive measures are proposed here: SM03, SM04. They require the local regulator to rigorously evaluate the profile of all 5G providers in the country and the EU. Restrictions should be applied, including the necessary exclusions in the area of 5G providers. The second preventive measure is the establishment of a legal and regulatory framework limiting the type of business and the conditions under which mobile network operators may outsource certain functions to providers outside their structures (MSP services). These measures should be implemented within two years.
Are the “5GEUtoolbox” tools mandatory?
The document was prepared and agreed upon by an executive group on network and information security composed of representatives of all Member State authorities, the Commission, and the EU Cybersecurity Agency. A coordinated EU approach in this regard is based on a strong commitment by all Member States and the Commission to use and fully implement a key set of recommended measures.
It means that the guidelines from this document are binding and will be subject to audits and necessary regulations. The government of the Republic of Poland is already working on regulations on the basis of which Polish regulatory and economic entities will cooperate with each other.
All Member States will have to assess the risk profile of 5G vendors taking into account the criteria set out in this document and, consequently, apply appropriate restrictions to vendors considered high risk, in relation to key assets identified as critical and sensitive.
In practice, the EU has not directly issued supplier-related bans, implicitly Chinese. This obligation has been delegated to the Member States.
In the case of the Polish government, we are waiting for guidelines for operators in the area of risk assessment of 5G suppliers. I am curious how the Polish government will handle this “hot potato”, created in cooperation with the EU.
Regardless of the guidelines of the Polish government, the document “5GEUtoolbox ” emphatically indicates mobile operators as entities undertaking operational activities in the field of cybersecurity and the operation of their networks. This does not change the fact that suppliers of telecommunications equipment and 5G telecommunications software take responsibility for providing appropriate products for operators, under pain of exclusion from the EU supply chain.
EU and other instruments protecting telecommunications networks.
Under the framework of the “EU Telecommunications Law”, various cybersecurity obligations may be imposed on telecommunications operators. Member States are required to ensure the integrity and security of public communications networks. This framework provides that national regulatory authorities have the power to issue binding instructions and ensure compliance with these criteria.
Another institution is the European Electronic Communications Code (EECC), which will be responsible for maintaining and expanding cybersecurity regulations. As of December 21, 2020, the EECC will replace the current BEREC regulations.
The last, but very important institution is the NIS, which, through the NIS Directive, requires service providers from other areas such as energy, finance, medical care, transport, or digital service providers to take appropriate security measures and report incidents to the competent national authorities. The directive also provides for the coordination of work between Member States in the event of cross-border incidents affecting operators in its scope.
The final instrument is the Law on cyberbezpieczeństwie (Cybersecurity Act), which entered into force in June 2019. And provides a framework for European certification systems cybersecurity products, processes, and services.
What are the next steps for the EU in cybersecurity?
In line with the recommendations of the NIS, the work will be continued within the framework of the Network and Information Security Cooperation Group, namely:
- By 30 April 2020, the Commission urges Member States to take concrete and measurable steps to implement a set of key measures.
- By 30 June 2020, the Commission invites the Network and Information Security Cooperation Group to prepare a status report on the implementation of these key measures in each Member State.
- By October 1, 2020, Member States, in cooperation with the European Commission, should assess the impact of the March 2019 Commission Recommendation to determine if there is a need for further action.
Summary
The creation of the “5GEUtoolbox ” document is the first concrete response of the EU to the strict requirements for the security of the 5G network set by the US administration. The set of rules does not directly indicate whether and how to prohibit access to infrastructure by Chinese companies. Instead, it calls upon specific bodies of national regulators to develop their own guidelines, in line with this document and their own safety guidelines.
There is no doubt, however, that it is the mobile operators that will be responsible for the operational protection of EU residents, as the above “5GEUtoolbox ” scrupulously indicates.
We will now be waiting impatiently for the next guidelines on key security measures and specific actions by individual mobile operators in Poland. The tender for the 5G band has started, so soon the operators will announce their decisions on the selection of suppliers, of course, based on the guidelines of the Polish government.
The material was prepared on the basis of the document ” Secure 5G networks: Questions and Answers on the EUtoolbox “.
